-������
- ����������� ������
- �������: 25500 �����������: 7
- ���� ������
- �������: 3347 �����������: 2
- ��������� ������.
- �������: 245200 �����������: 1
- ������ �. ��������.
- �������: 48625 �����������: 2
- �� ��� ���� - ���� ��������
- �������: 79338 �����������: 0
-�������
- ������� (578)
- ����� (46)
- ������� (35)
- ������ (18)
- ����� (16)
- �������,�������,������������� (13)
- ����� (12)
- ������� (5)
- ������ (3)
- ��������,�������� � ��. (2)
- ��������� ������� (1)
- ��� ������� (1)
- �������� (1)
- ������� (381)
- �������� ������� (218)
- ������ ������� (165)
- ��������� (348)
- ������ ��� ���� (245)
- ������� (125)
- ���� �� ����� (23)
- ����� (13)
- �������������� (10)
- �������� ������ ������ (8)
- ��������� (2)
- ������� (1)
- ������� (1)
- ������� (274)
- ����� (232)
- ������� ������� (216)
- ������� ������ (14)
- ������� ������ (12)
- ������� (2)
- ������-����� (221)
- ��� ���������� (96)
- ������� (84)
- �������� ������� � ����� (47)
- ������� ������� � ������� (37)
- ��������� (74)
- ��������������� (42)
- ������� (17)
- ������������� (61)
- �������� � �������� (57)
- ��� ��� ���������� ������ � ��������� (52)
- ��������� ��� ��������� (41)
- ���� (16)
- �������� (9)
- ��� ���� ����� (5)
- ������ (4)
- ��� �������� (4)
-� - ��������
-����� �� ��������
-���������� ��������
-����������
-����������
�������: 2124
������������: 1392
��������: 3875
����-���� � ������������� Windows ... |
***
� ������ �������������� �������: «��������� � �������������!..».
� ��������� ����� ����������� ���� ���������� ����������� ��������-�����������, ��������� ��������� �� �������� ����� sms-��������� ��� ��������� ������� � ��������������� ������� ��� � ���������������� ������ (��������� ������ ��������� – � �������� ���������� ����� ������).
8 ������ 2009 �. �������� «������ ���» �������� � ��������� ������ ������� �������� ��������� ���������, ������� ��� ������� Windows ���������� ������ «��������������� ���» – ����� ��� ����������� �������������� ����� Windows. ��� ������������� ������� � ������� (����� ��� ��������� ���������������� ����) ��������� ��������� ������� sms-��������� – � ��������� ������� (������������������ ��������� ����) �� ��������� �����.
��������� ����� ���������: «Windows ������������. ��� ������������� ���������� ��������� ��� � ������� 4128800256 �� ����� 3649. ������� �������������� ������� ����� �������� � ������ ������ ���������� � ���������� ������ ����������».
� ���� �������� ��������� ���� ������ ���������� ��� � ������ ���������.
***
��� ������������ ����� �����, ����������� ������ Windows
������ ����������� ��������� ���� ��������� � �������� ���� Dr.Web 08.04.2009 �., ��� ��������� Trojan.Winlock.19. �� ����������� ������������� ������������ ����������� Origins TracingTM ��� Trojan.Winlock.origin.
��������� ����������� ���������� ����� � 13.04.2009 �., ��� Trojan-Dropper.Win32.Blocker.a � Trojan-Ransom.Win32.Agent.af.
Panda Security � 20.04.2009 �. �������������� �����, ��� Trj/SMSlock.A.
�����-����������� �������� �� �� �������������, ��� �������, ��� ����� ������������, ����������� ���� ��� �����������.
����� ������������ ����� ��������� ���������, ��������������� � ������� ������ ����������� ���������, ������� ��������� ������ ������������ ������� Windows.
��������� �������� ����������� Windows (PE EXE-����). ����� ������ 88576 ����. �������� �� C++.
***
������������� �������� ������
����� ��������� ����� ��������� �� ������ ���� ���� �� ��������� ������� �������� ������������ Windows – %Temp%\<rnd>.tmp (<rnd> – ��������� ������������������ ���� � ���� ���������� ��������).
������ ���� ����� ������ 94208 ����.
����� ��������� ���������� ���� ����������� �� ����������, �������� ��������� ��������:
– ��� ��������������� ������� � ������� [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon] ���������� ������� ����� �������� �������� ���������� (REG_SZ) ��������� Userinit – �� %Temp%\<rnd>.tmp;
– � ����������� �� ������� ���� ����� ���������� http-������: http://%3Crnd1%3E.com/regis***.php?guid={<rnd2>}&wid=<rnd3>&u=<rnd3>&number=<rnd4>install=1,
��� <rnd1> – url-������, �������������� �� ������������ ��������� � ����������� �� ������� ����;
<rnd2> – ���������� �������������� ���������� �������������;
<rnd3> – ��������� �����;
<rnd4> – �������� ����� �������� �����;
– ����� ������������ �� ����� ������� ���� � ������������ ��������� sms-��������� �� ��������� ����� ��� �������������;
– ��� ��������������� ������������ ������� Windows � ������� �������� ������ ��������� ���� ���������� �������������� ��� ������ a.bat. � ������ ���� ������������ ��� ��� �������� ������������� ����� ������ � ������ ����� ���������� ��������������;
– ����� ���� a.bat ����������� �� ���������� (������, ���� ����� «������� � ������������»: ����� 2 ���� ����� ������� �� ������ ���� «��������», �� ���� ����������������, ���� � ������� 2-� ����� ��� ������������� �� ������).
***
��� �������������� Windows
• ��� ������ ������������� Windows, ��������������� ������� Trojan.Winlock, �� ������ ��������������� ������, ������������� ������������� «������ ���»:
– � ��������� ���� ����� ��� SMS ������� ����� sms (� ������ �������� ��������������� �������), ������� ������ OK;
– � ��������� ���� ��� ��������� �������� ���, ������� ����� ������ � ��������� ���� ������ ���������� ��� �� ��������������� �������.
|
|
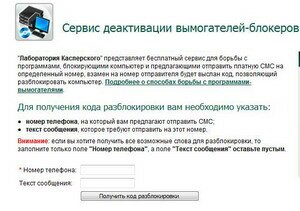
• «����������� �����������» �� �������� � ������� � ��������� ���������� online-������ ������������� ���������� ��:
– ������� �� �������� ������ ����������� �����������-�������� «����������� �����������»;
– � ��������������� ��������� ���� ������� ����� �������� (�� ������� ��� ������������ ��������� SMS) � ����� ���������, ������� ��������� ��������� �� ���� �����;
– ������� ������ �������� ��� �������������:
***
��� ������� ����� �������
��������� Windows � ��� ���������� «������ �����», ��������, ���������������� ����������� ��������-����������������� ������, ���� Windows miniPE ��� ERD Commander:
– �������� ���� � ERD Commander � ����� CD-ROM, ������������� ��;
– �� ����� ������������ ������� Delete ��� ����� � CMOS Setup Utility;
– ���������� �������� �� � CD-ROM, ������� F10, �������������� ��������� ���������, �������� ������������;
– � ����������� ���� ������ �������������� Windows XP �������� �������� ERD Commander –> Enter;
– ����� �������� ������ ��������� Starting Winternals ERD Commander;
– ����� �������� �������� ���������� � ����������� ���� ������� ������ Skip Network Configuration;
– � ���� Welcome to ERD Commander �������� ���� �� –> OK;
– ����� ���������� ������� ����, ������ �������� ������ My Computer;
– � ���� ERD Commander Explorer ��������� ����, �� ������� ����������� �� (��� �������, C:\);
– ������� ������������ ���� ������, ��� �������, �� ���������� �� ��������� �������� �������� ������������ Windows – %Temp%\<rnd>.tmp (����� ����� �������� �������, ���������, ������ ������);
– �������� ���� ERD Commander Explorer;
– ������� Start –> Administrative Tools –> RegEdit;
– � ���� ERD Commander Registry Editor ������� ������ [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon];
– ��������� �������� ���������� REG_SZ-��������� Userinit �� C:\WINDOWS\system32\userinit.exe, (���� ������� ����������� �� ����� C:\, ���� �� ������ �����, �� <�����_�����>:\Windows\system32\userinit.exe,). ����� ������������� �������� ����� ��������� %Temp%\<rnd>.tmp;
– � ���� �� ������� ��������� (��� �������������) �������� ���������� REG_SZ-��������� Shell �� Explorer.exe;
– �������� ���� ERD Commander Registry Editor;
– ������� Start –> Log Off –> Restart –> OK;
– �� ����� ������������ ������� Delete ��� ����� � CMOS Setup Utility;
– ���������� �������� �� � ����������, ������� F10, �������������� ��������� ���������, �������� ������������;
– ��������� Windows � ������� ������;
– ��������� ������� ����������� �� ������� ������.
����������
1. ��������! �� ������������ �� ������ ���������������, – �� ����������� sms �� ���������� ������, �� ������ ������ �����������, ��������� �����.
2. ������, ������������ ���� ������-������������, ��� �������, ������� «������������ ���������������� �����������», � ������� ����������� ����������� ���������� ��. ������������ ���������� ����������� ����������� �� ��������� �������� �� ���� ��: ��� ������ ��� ��������� �������� ��� ����� ������������ ����������? ��� �����, ��� ��������� ������ ������-������������ ����������� �� ��������� ������ �������-������ �������� ������������ � ���������������� �����������, ��������� ��� ���� �� ��������� ������ (��� �� ����� �� ��������� ���!), � ����� ������������� ��������������� � �������. �� � ����� ������ ������������ ������������� �������� � ������� ���!..
3. �������, ��� ������������ �����, ��� ������! ����������� ������������� � ��������� ������������� ����������� � ��������� (�� ����� ������ ���� � ������!) ������������ ������.
������� �������
***
• «������ ���» �������� ���������� �� �������, ������������ ������ � �������
• Ransomware Reloaded – PandaLabs
• Trojan-Dropper.Win32.Blocker.a
| �������: | ��������� ��� ��������� |
| �������������� | « ����. ������ — � �������� — ����. ������ » | ��������: [1] [�����] |







