��������� Cisco AnyConnect VPN with 2FA (ActiveDirectory and Certificate) ����� ASDM |
����� ���� ��������, � �� ��������� ���������� ������� �� ���� ����, ��� ����� � ASDM or console: �� ���� � ���� ��� ���������� ������� ����������� ASDM � ��������� ������ ����� ��������� ������ ����� ���. ������� ������ ����� ��������� ���������� (��������)
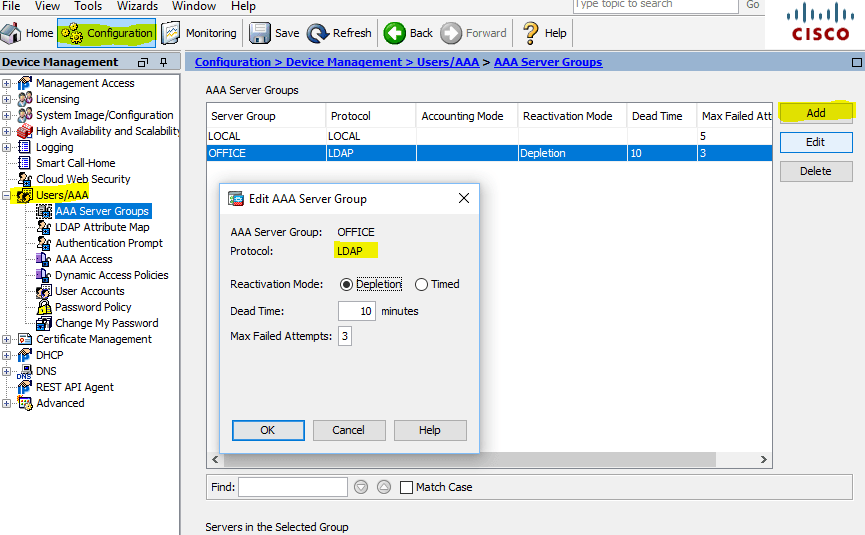
����, ���������. ������ � ��������� LDAP ������� (� ����� ������ ��� DC ActiveDirectory), ��� ����� ��������� � Configuration > DeviceManagement > Users/AAA > AAA Server Groups � ������� ������, ������� �� OFFICE, Protocol ��������� LDAP
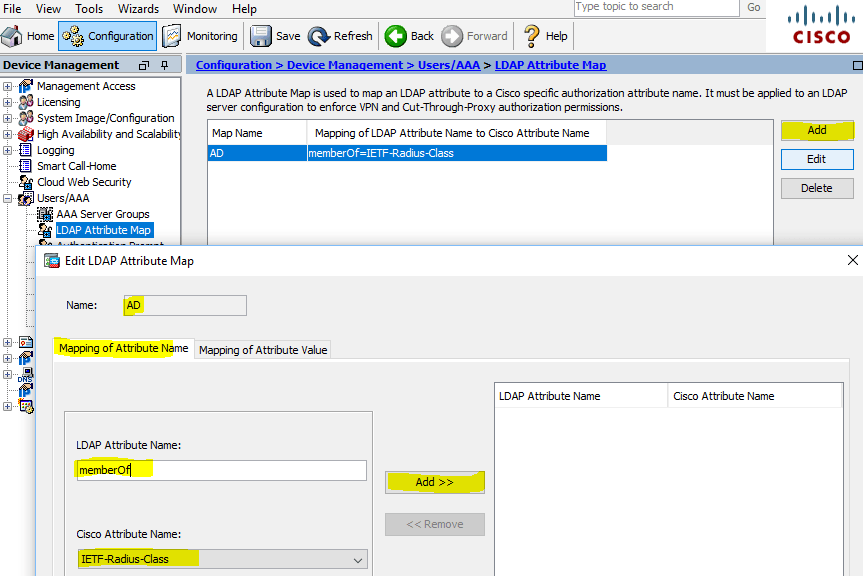
��� ����, ����� �������� ������ � ��������� ������, ��� ���������� �������������� ������� LDAP Atribute Map. ��� ����� ��������� � ��������������� ������: Configuration > DeviceManagement > Users/AAA >LDAP Attribute Map � ������� ����� �����: � ����� ������ ��� Map Name: AD, Mapping of Attribute Name > LDAP Attribute Name: memberOf, Cisco Attribute Name: IETF-Radius-Class
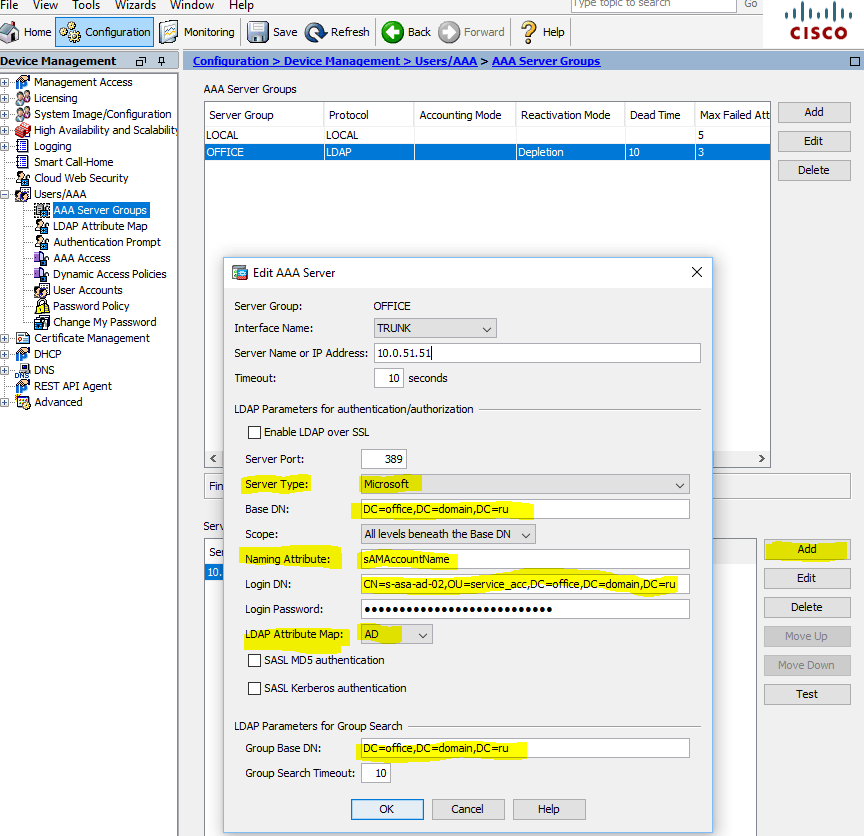
������ ����� �������� ������ (��������� ����������� � ����������� ������), ��������� ���������, ����� ������� ����� ������������, IP ����� DC, Server Type: Microsoft, Base DN, Naming Attribute: sAMAccountName, Login DN, Login Password, ������ ��� ��������� ����� LDAP Attribute Map: AD, Group Base DN:
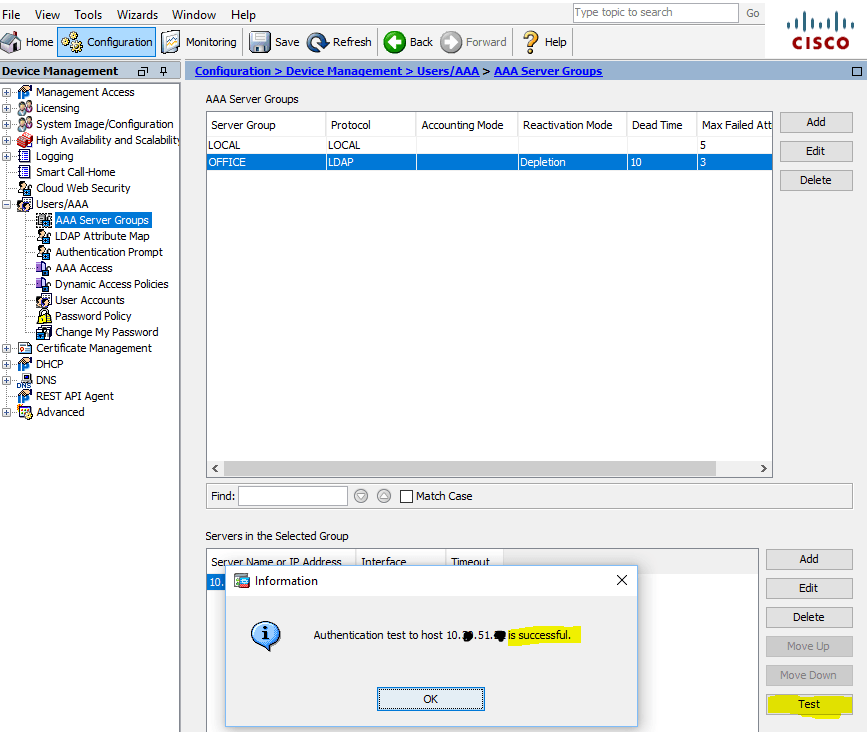
����� ���������� ������� ������ ��������, �������� �������������� ������� ������� AD:
������ ����� �������� ���������� ��������������� ������ (������������ Microsoft CA, � ������ ������ � ��� ��������� ������������ �� ����, ������������ � ��� ������� ����������� �������: Cisco ASA �� ������������ ����������� � Signature algorithm RSASSA-PSS, ������� Microsoft ���������� ������������ �� ���������. �� ������ �� sha512RSA):

��������� Configuration > DeviceManagement >Certificate Management > Identity Certificates � ����������� � ������� PKCS12 (*.pfx ���������� + private key):

� ����������������� ���������� ���������, ����� ���������� � ��������� �������� ��� AnyConnect VPN. ��� �������, ����� ������������ 2 �������, � ������� ����� ������ IP Address Pools � �����. ACL, Dynamic Access Policies, Group Policies � �������������� 2 ������ ActiveDirectory. ��� ����������� ������������� �� ��� ���������� �������� ��������������� ������ ��������� �����, ��� ���������� Split Tunneling, ����� �� ����� ���� ���������������� ������� ����� ���. �� ��� ��� ���������, ����� ����-��, ��������, ����� ����������� � ��������� ����� ��� ����� ��������� ;)
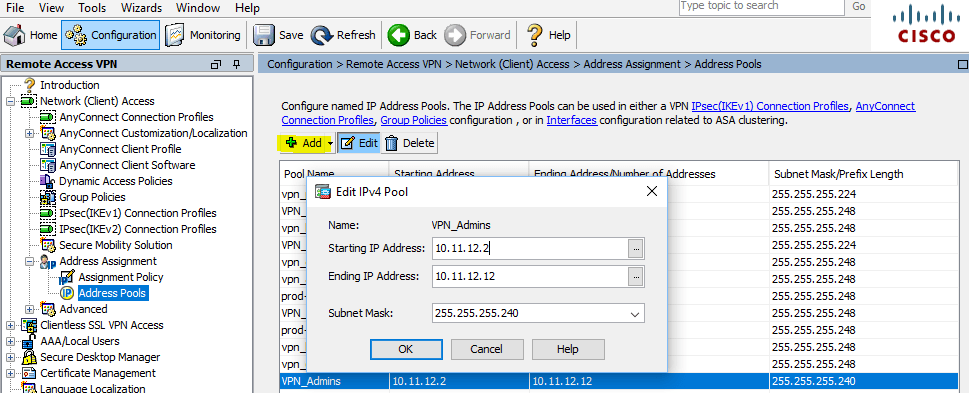
������ � IP Address Pools, ��� ����� ��������� � Configuration > Remote Access VPN > Network (Client) Access > Address Assignment > Address Pools
�������� ��� ������� (�������) ��� ��������������� (�������, �������� VPN_Admins):
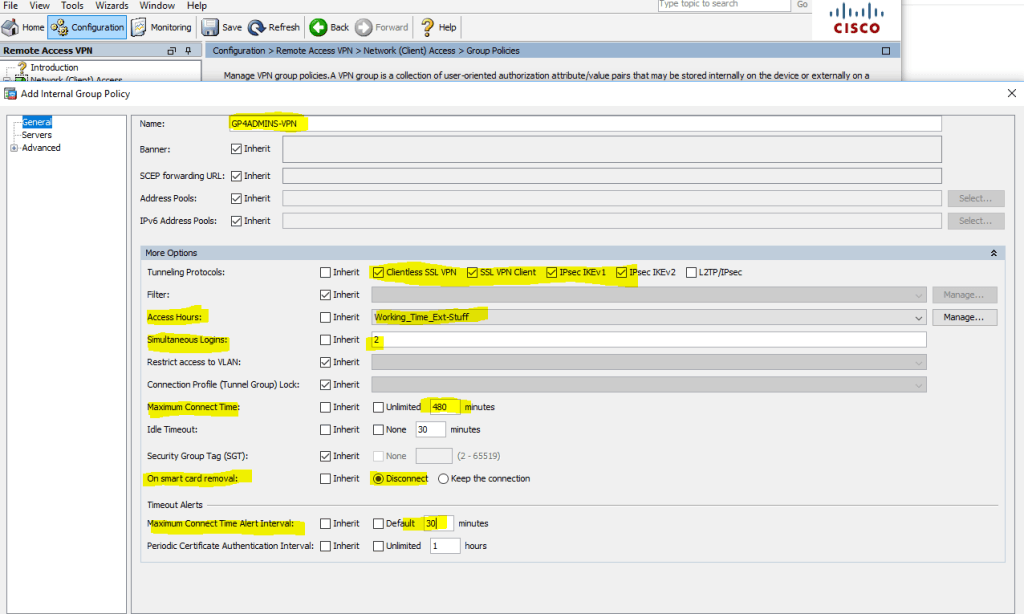
����� �������� �������� (��� �������� ����� ��������� �������, � ������� ����� �����: ���������, ������� ����� �������������� ��� ��������, ����� �������, ���������� ������������� �������, ������� ������� � ������������ VLAN, ��������� ��������, ������ DNS �������, ��������� Split Tunneling, ���������� ��������� � �� � ��) � � ����� ���� ��������� ������� ������� ������ ��������! ����, ������: Configuration > Remote Access VPN > Network (Client) Access > Group Policies, Add Internal Group Policy
��� ������������ ��������� ������ ������������� � � ����� ������ ������� ������������� ������� ���������, ������� ����������� ��� �������� ������� (Tunneling Protocols), ��������� ������ ��� ������� �� ��� (Access Hours), ���������� ������������� ����������� � ����� ������� ������� (Simultaneous Logins), ������������ ����� ��� ������ � ��.:
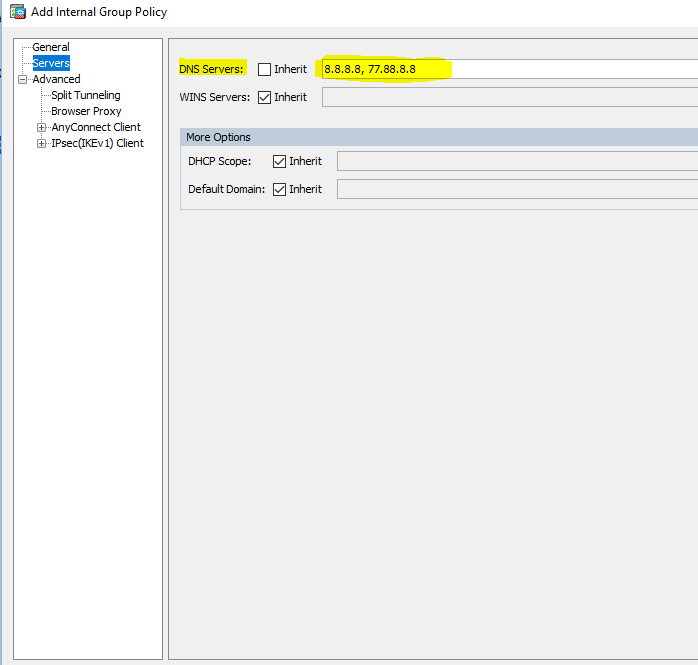
��������� �������� ��������� � ������� Servers, � ������� �� ����� ������� �����. ��� �������, ��� ������������� ��� AnyConnect, ����� ��� ����� ���������� � ���������� �������� �� �����:
������ �������� � ��� ����� ���������� ����� � ��������� Split Tunneling. ��� � ��� ����� ����� � ����� ������������ �������� ��������������� ������ ��������� ����� (�� �� ������������ � ������� ���� ������� ������������� � ��������� ������ � ��������� �������� � ����� �Local Lan Access� ����� ����� �������� �����������):
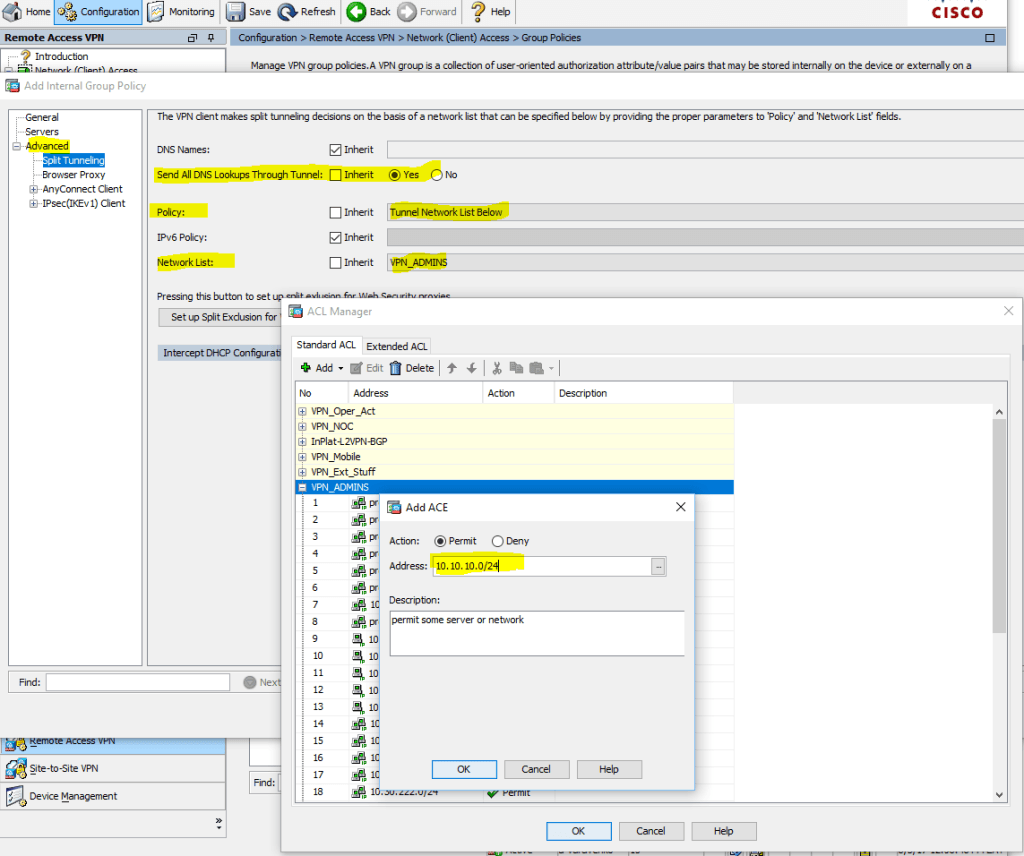
����� �� ������� � ����� �����\������ �� ��������� ������, ������ ��������� ������ � ��� �� ����������\������ (��� ���� ACL):

� �����, ����� ����������� � ��� AnyConnect ��������, ����� ������� �������� � ������� ������� � ������� ����������:

������ ����� ������� ��������������� � �������� ������� AnyConnect, ��������� Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles >, Add AnyConnect Connection Profile
� ���������: Name, Aliases, ����� Authentication Method (AAA and certificate), AAA Server Group, Client Address Pools, Group Policy � ��� ��������� �����!

� ������ ��������� �������� � �� �� ����������������� ����������� ������� �������� E-mail � � ������� ���������

����� ������� ��������� � �� ��� ����� ������������, ������ ��� ����� ������������ �������� �� ��������� DfltAccessPolicy ��� ���� �������������, ��������� �������������� (� ��� ����� ������� ���������). �� �� �����, ����� ��� ������ ����� ActiveDirectory ������������� ���� ������� � ������������ ���� ��������� �������� \ �������� �������. �������, ���������: Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies � ��������� DfltAccessPolicy (�� ����� ���� �� ���������, � ������ Terminate � ������������ ������������ � ������� ����������� ����, ��� ������������ �� ������� � ������ ������ ActiveDirectory):
����� ����, ��� �������� �� ��������� ���������, � �������� �����:
Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies > Add Dynamic Access Policy

��� g_vpn_level_01 � ��������� � ActiveDirectory ������ ������������, ���� �� �������� ����������� ��������� ������, ��� ����������� �� ��� AnyConnect � �������� VPN-ADMINS:

�� � �������������� ������� � ���������� ��������� ��������� ������� � ���� (�������, ��������, ��� ������������� �������� ��� StandBy unit ��� Failover ������������):
����� ����, ��� ������� �������� � ��� ����� ������� ���������������: ������� � ������� ��� �����"Local Lan Access"? ��� ��� ��� ����� �������������. � ��� ����� �� ����� ��������� ����� ��������� ������������, �������������� ������� AnyConnect, ���������\��������� ����������� ����������� � ����� ����� ���, ��� ������������ ���, ������� ������ ��������� (IPv4 or IPv6 or both, ��������� ������������ � ��������, ��������� ��������. � ����� ���� ��� ������������ ��� ���� �����!
��� ������ ������ � �VPN-USERS� ����������� ���� �����
P.S. ��� ��������� ������� � ������ ������������ �����
�����:
author VFedorV
������� ����������
cisco
cisco asa
anyconnect
asdm
����, ���������. ������ � ��������� LDAP ������� (� ����� ������ ��� DC ActiveDirectory), ��� ����� ��������� � Configuration > DeviceManagement > Users/AAA > AAA Server Groups � ������� ������, ������� �� OFFICE, Protocol ��������� LDAP
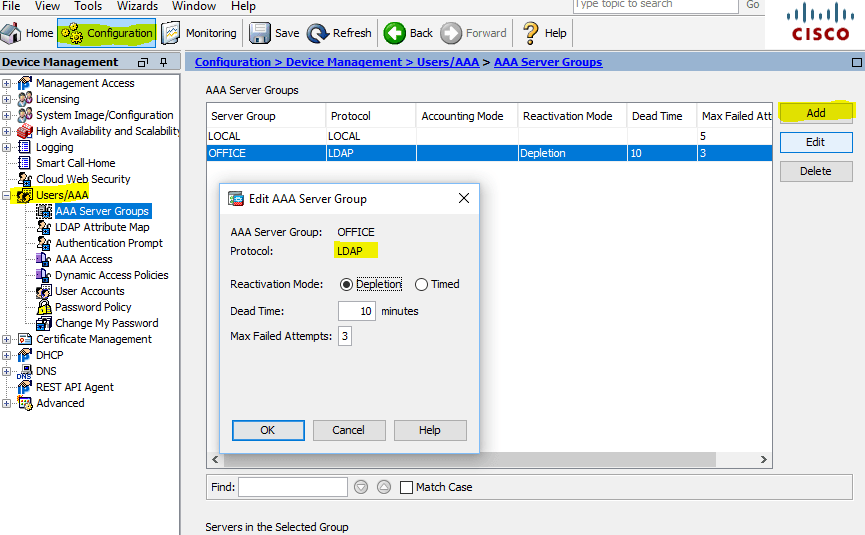
Configuration Cisco ASA AAA Server Groups
��� ����, ����� �������� ������ � ��������� ������, ��� ���������� �������������� ������� LDAP Atribute Map. ��� ����� ��������� � ��������������� ������: Configuration > DeviceManagement > Users/AAA >LDAP Attribute Map � ������� ����� �����: � ����� ������ ��� Map Name: AD, Mapping of Attribute Name > LDAP Attribute Name: memberOf, Cisco Attribute Name: IETF-Radius-Class
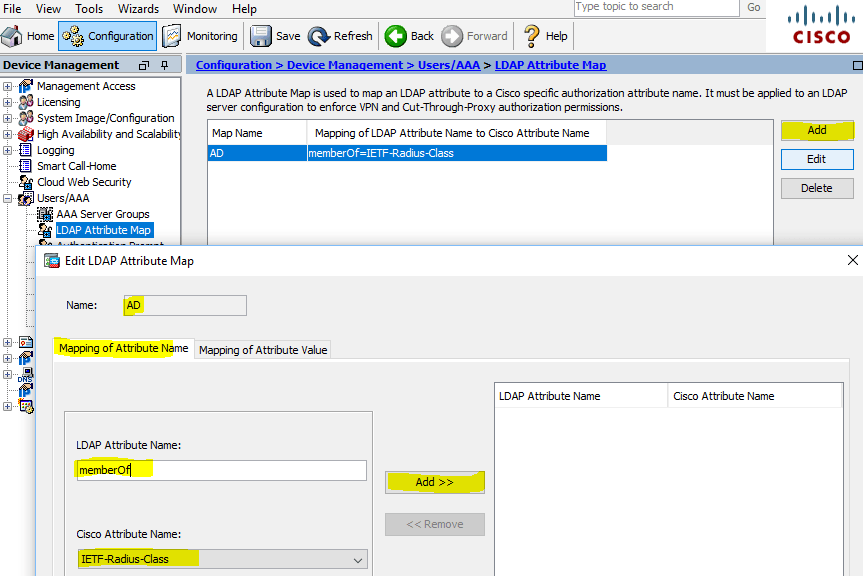
LDAP Attribute Map
������ ����� �������� ������ (��������� ����������� � ����������� ������), ��������� ���������, ����� ������� ����� ������������, IP ����� DC, Server Type: Microsoft, Base DN, Naming Attribute: sAMAccountName, Login DN, Login Password, ������ ��� ��������� ����� LDAP Attribute Map: AD, Group Base DN:
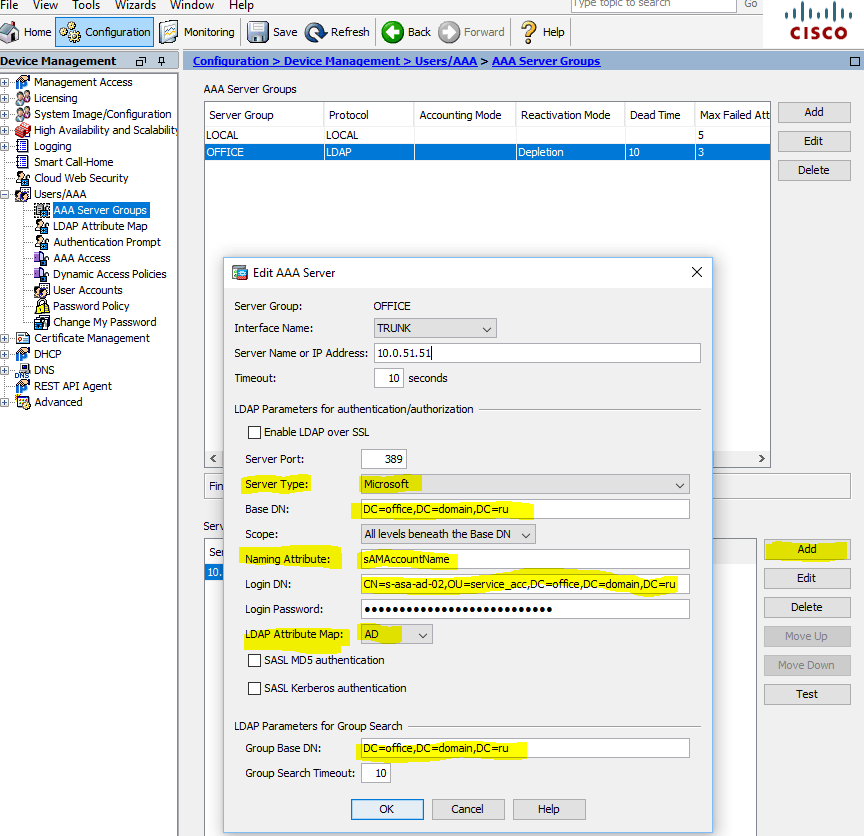
AAA Server � Microsoft DC
Add AAA Server
����� ���������� ������� ������ ��������, �������� �������������� ������� ������� AD:
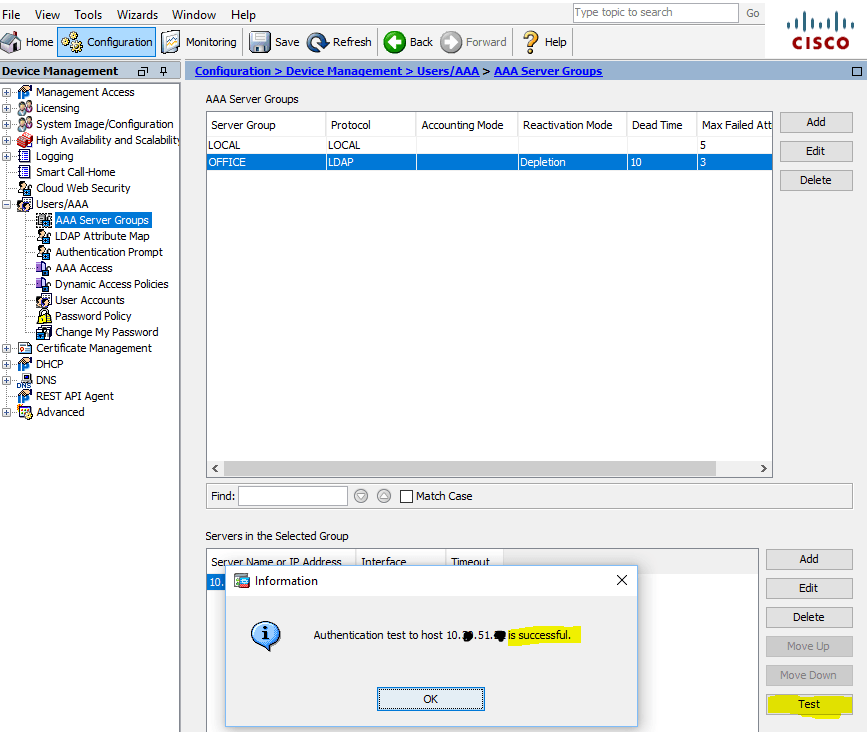
Test AAA Server � Authentication
������ ����� �������� ���������� ��������������� ������ (������������ Microsoft CA, � ������ ������ � ��� ��������� ������������ �� ����, ������������ � ��� ������� ����������� �������: Cisco ASA �� ������������ ����������� � Signature algorithm RSASSA-PSS, ������� Microsoft ���������� ������������ �� ���������. �� ������ �� sha512RSA):

Identity Certificates Signature algorithm RSASSA-PSS � sha512
��������� Configuration > DeviceManagement >Certificate Management > Identity Certificates � ����������� � ������� PKCS12 (*.pfx ���������� + private key):

Identity Certificates Signature algorithm sha512RSA (ECDSA 521 bits)
� ����������������� ���������� ���������, ����� ���������� � ��������� �������� ��� AnyConnect VPN. ��� �������, ����� ������������ 2 �������, � ������� ����� ������ IP Address Pools � �����. ACL, Dynamic Access Policies, Group Policies � �������������� 2 ������ ActiveDirectory. ��� ����������� ������������� �� ��� ���������� �������� ��������������� ������ ��������� �����, ��� ���������� Split Tunneling, ����� �� ����� ���� ���������������� ������� ����� ���. �� ��� ��� ���������, ����� ����-��, ��������, ����� ����������� � ��������� ����� ��� ����� ��������� ;)
������ � IP Address Pools, ��� ����� ��������� � Configuration > Remote Access VPN > Network (Client) Access > Address Assignment > Address Pools
�������� ��� ������� (�������) ��� ��������������� (�������, �������� VPN_Admins):
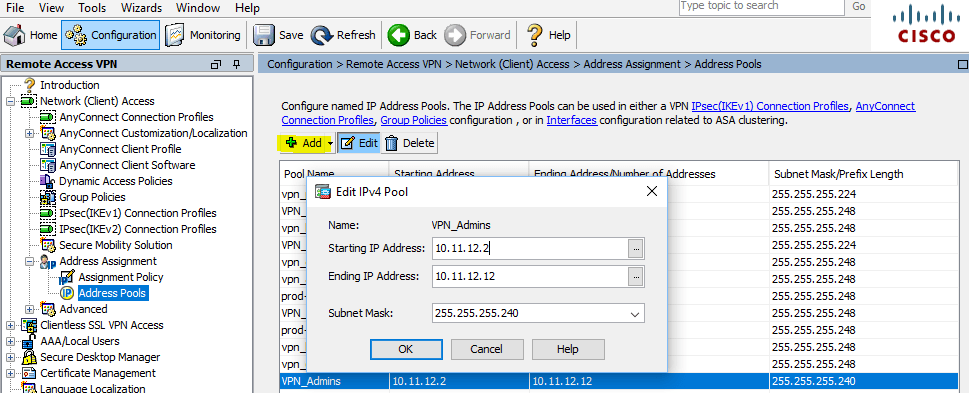
Address Assignment � Address Pools
����� �������� �������� (��� �������� ����� ��������� �������, � ������� ����� �����: ���������, ������� ����� �������������� ��� ��������, ����� �������, ���������� ������������� �������, ������� ������� � ������������ VLAN, ��������� ��������, ������ DNS �������, ��������� Split Tunneling, ���������� ��������� � �� � ��) � � ����� ���� ��������� ������� ������� ������ ��������! ����, ������: Configuration > Remote Access VPN > Network (Client) Access > Group Policies, Add Internal Group Policy
��� ������������ ��������� ������ ������������� � � ����� ������ ������� ������������� ������� ���������, ������� ����������� ��� �������� ������� (Tunneling Protocols), ��������� ������ ��� ������� �� ��� (Access Hours), ���������� ������������� ����������� � ����� ������� ������� (Simultaneous Logins), ������������ ����� ��� ������ � ��.:
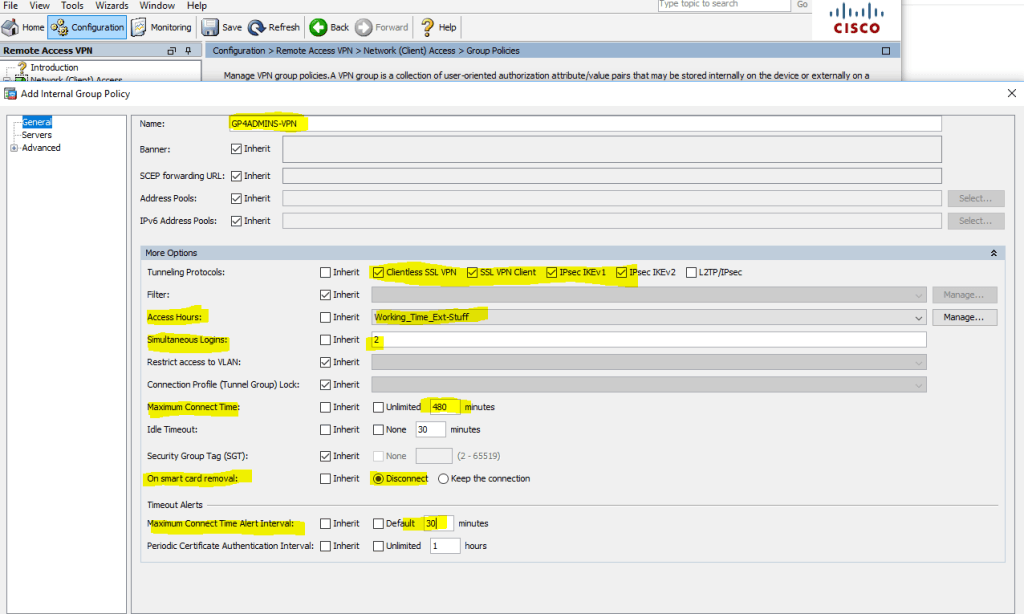
Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Add Internal Group Policy
��������� �������� ��������� � ������� Servers, � ������� �� ����� ������� �����. ��� �������, ��� ������������� ��� AnyConnect, ����� ��� ����� ���������� � ���������� �������� �� �����:
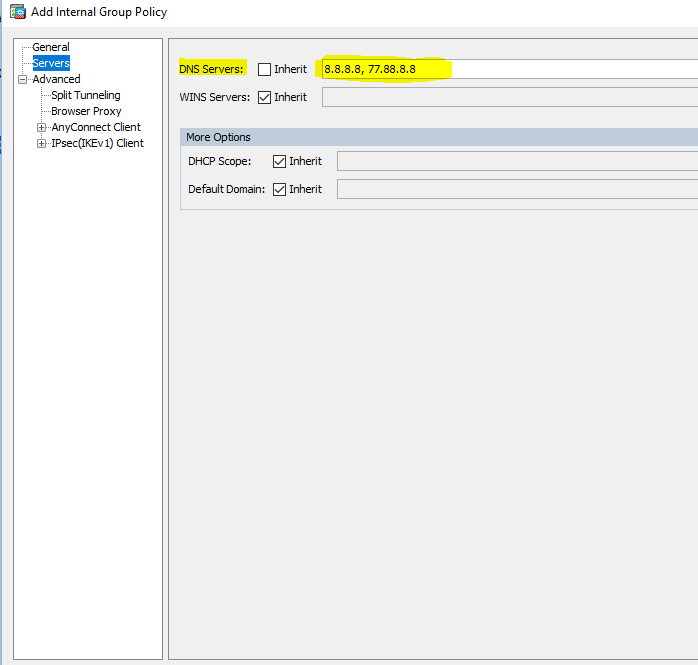
Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Edit Internal Group Policy � Servers
������ �������� � ��� ����� ���������� ����� � ��������� Split Tunneling. ��� � ��� ����� ����� � ����� ������������ �������� ��������������� ������ ��������� ����� (�� �� ������������ � ������� ���� ������� ������������� � ��������� ������ � ��������� �������� � ����� �Local Lan Access� ����� ����� �������� �����������):
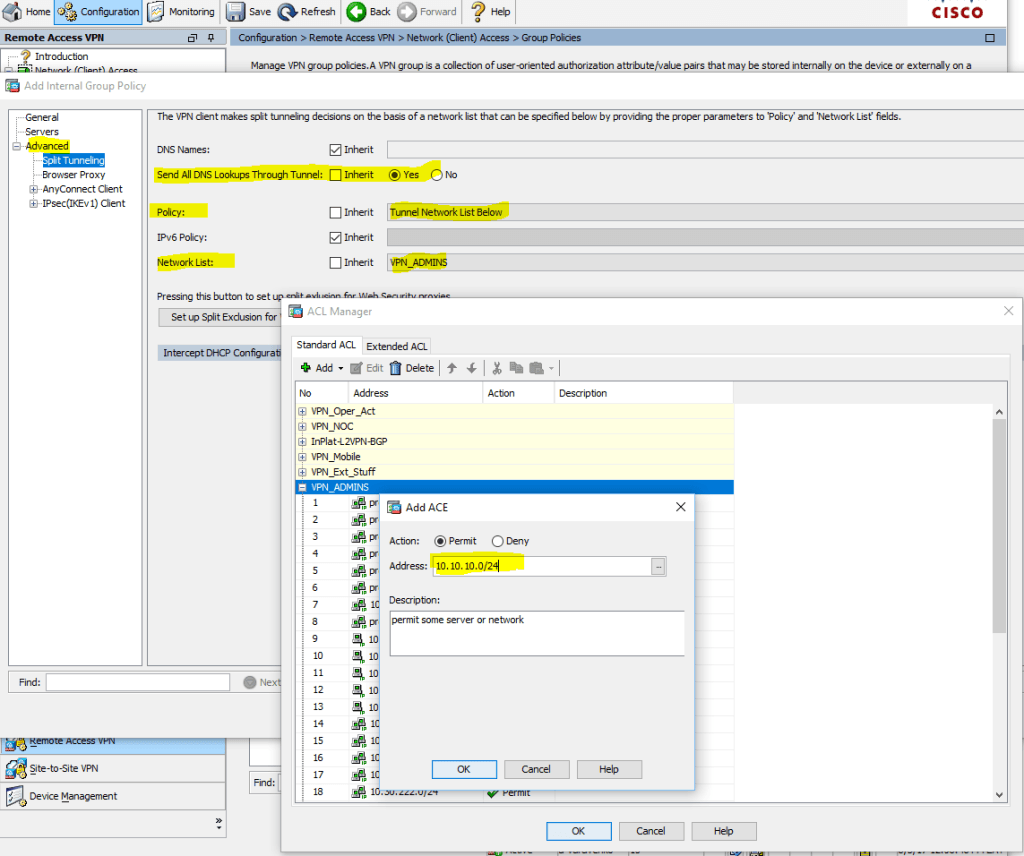
Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Edit Internal Group Policy > Advanced > Split Tunneling >
����� �� ������� � ����� �����\������ �� ��������� ������, ������ ��������� ������ � ��� �� ����������\������ (��� ���� ACL):

Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Edit Internal Group Policy > Advanced > AnyConnect Client > Client Firewall > Private Network Rule
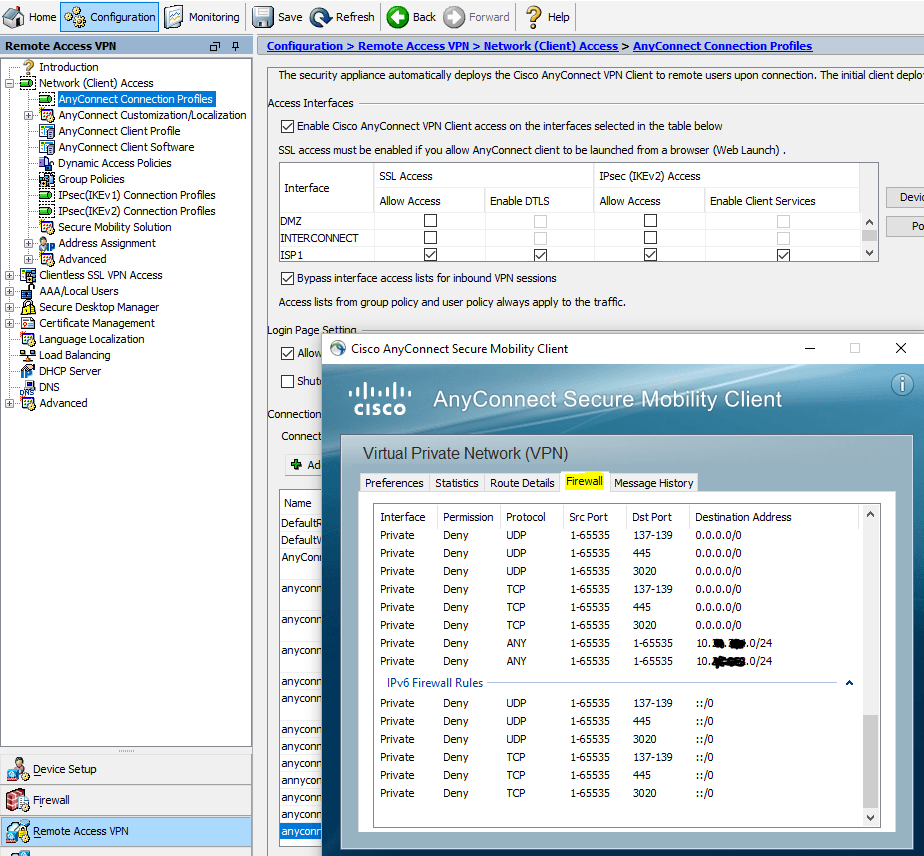
� �����, ����� ����������� � ��� AnyConnect ��������, ����� ������� �������� � ������� ������� � ������� ����������:

AnyConnect Client > Route Details
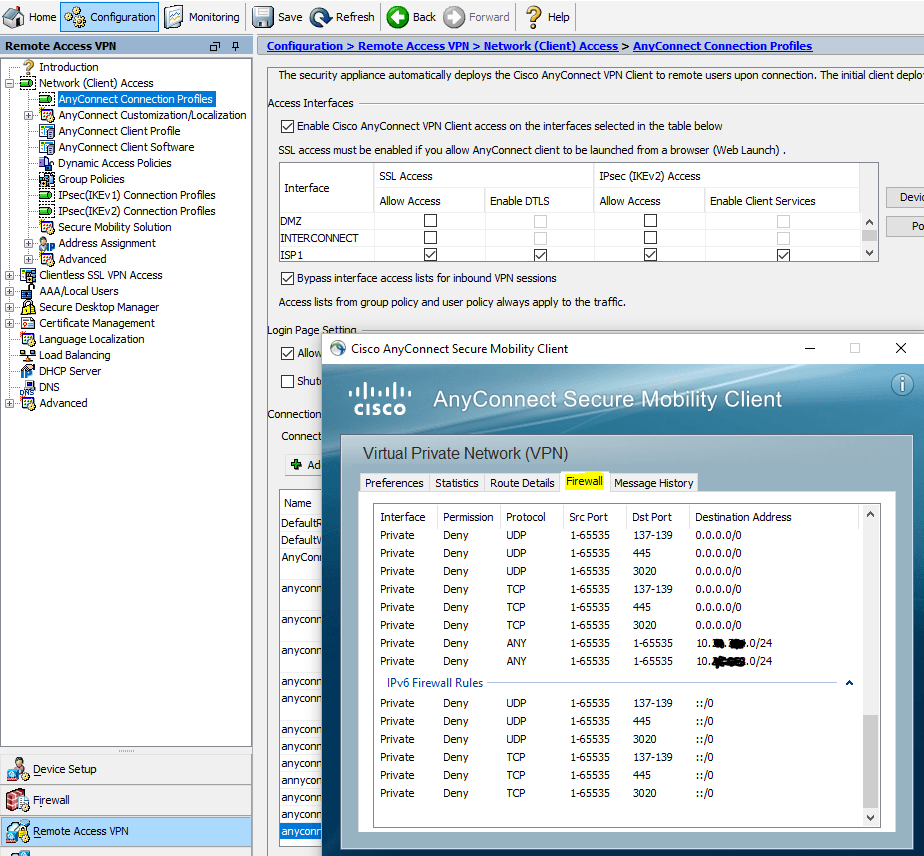
AnyConnect Client > Firewall
������ ����� ������� ��������������� � �������� ������� AnyConnect, ��������� Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles >, Add AnyConnect Connection Profile
� ���������: Name, Aliases, ����� Authentication Method (AAA and certificate), AAA Server Group, Client Address Pools, Group Policy � ��� ��������� �����!

Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles > Add AnyConnect Connection Profile > Basic
� ������ ��������� �������� � �� �� ����������������� ����������� ������� �������� E-mail � � ������� ���������
(.*)@������� �� ����
domain.ru(�������� E-mail ������ ����
%AD username%@somedomain.ru) � ��������� ��� � ���� Username ��� �����������.

Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles > Add AnyConnect Connection Profile > Advanced > Authentication > Username Mapping from Certificate
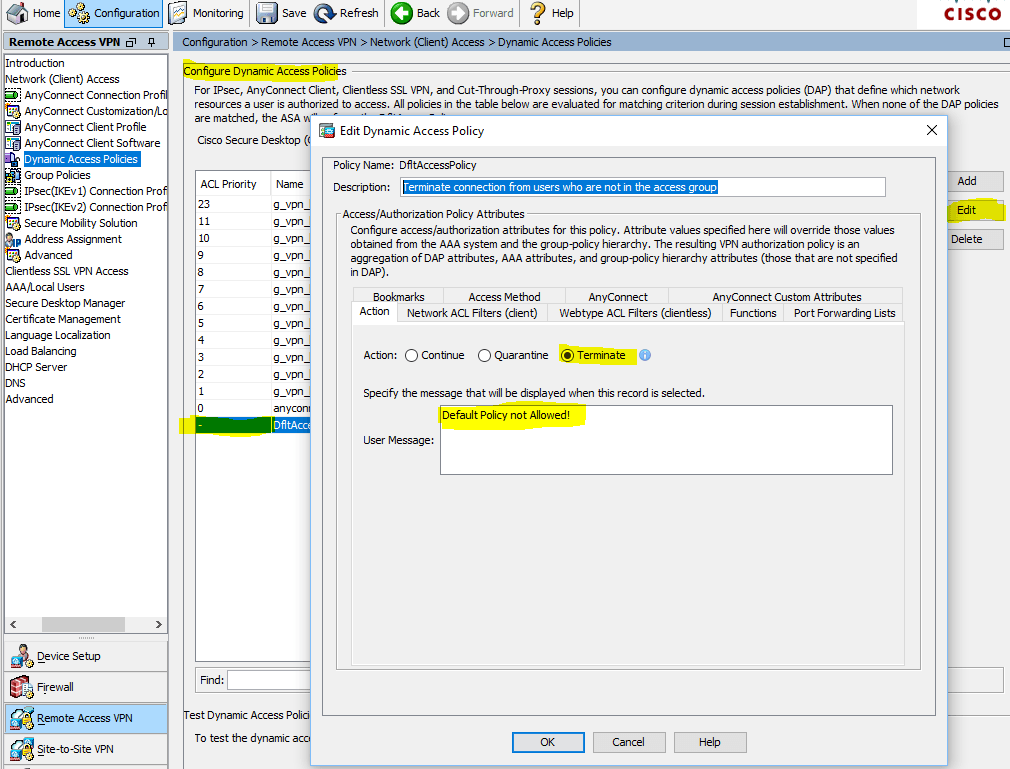
����� ������� ��������� � �� ��� ����� ������������, ������ ��� ����� ������������ �������� �� ��������� DfltAccessPolicy ��� ���� �������������, ��������� �������������� (� ��� ����� ������� ���������). �� �� �����, ����� ��� ������ ����� ActiveDirectory ������������� ���� ������� � ������������ ���� ��������� �������� \ �������� �������. �������, ���������: Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies � ��������� DfltAccessPolicy (�� ����� ���� �� ���������, � ������ Terminate � ������������ ������������ � ������� ����������� ����, ��� ������������ �� ������� � ������ ������ ActiveDirectory):
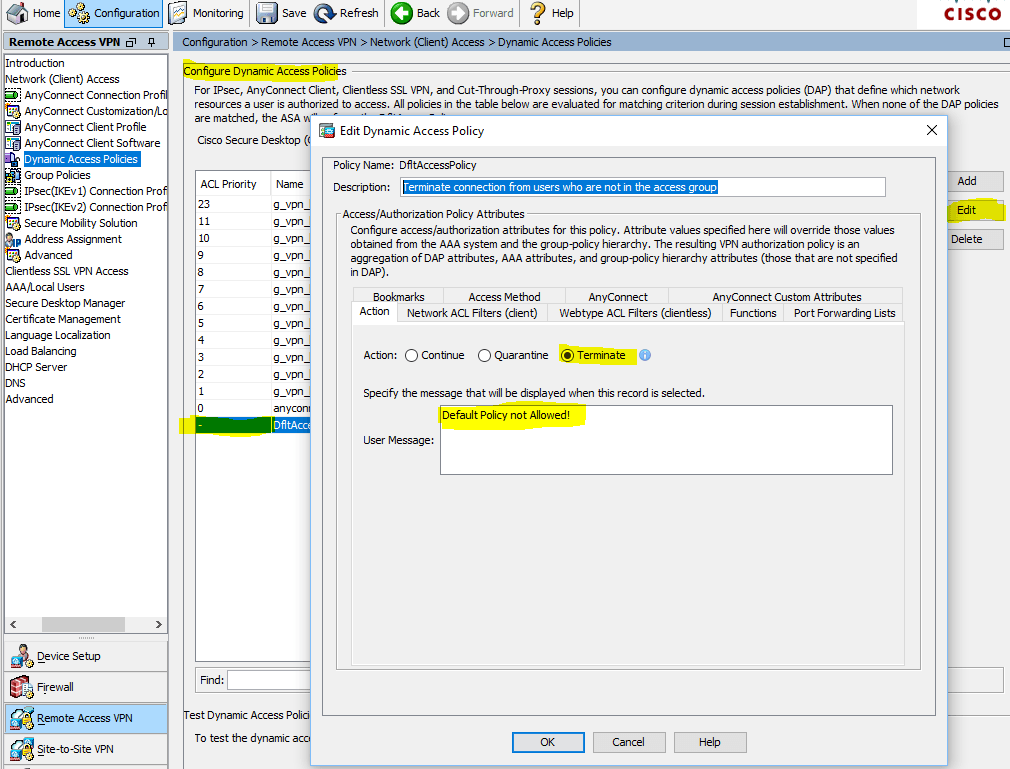
Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies
Terminate connection from users who are not in the access group
����� ����, ��� �������� �� ��������� ���������, � �������� �����:
Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies > Add Dynamic Access Policy

Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies > Add Dynamic Access Policy with AAA Attributes
��� g_vpn_level_01 � ��������� � ActiveDirectory ������ ������������, ���� �� �������� ����������� ��������� ������, ��� ����������� �� ��� AnyConnect � �������� VPN-ADMINS:

Configuration > Remote Access VPN > Network (Client) Access > Dynamic Access Policies > Add Dynamic Access Policy with AAA Attributes > Get AD Groups
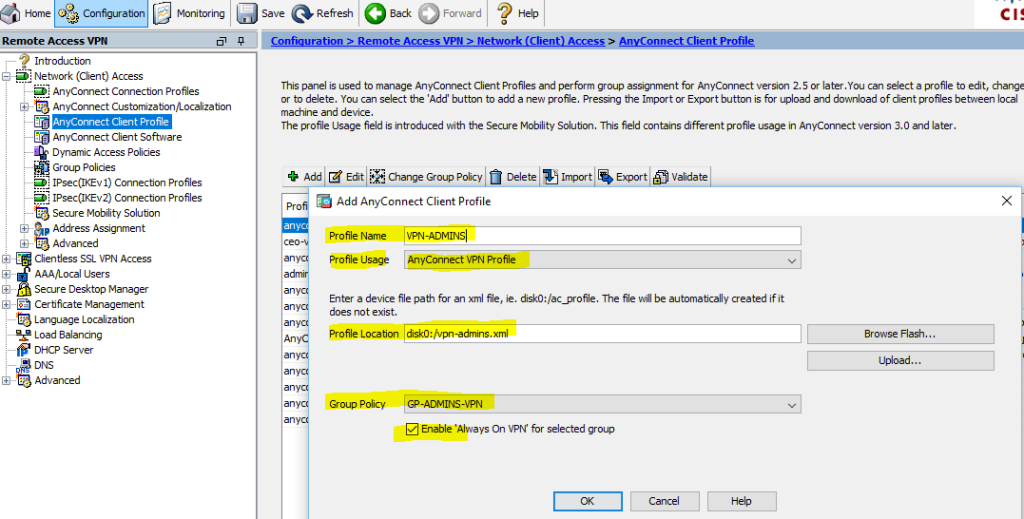
�� � �������������� ������� � ���������� ��������� ��������� ������� � ���� (�������, ��������, ��� ������������� �������� ��� StandBy unit ��� Failover ������������):
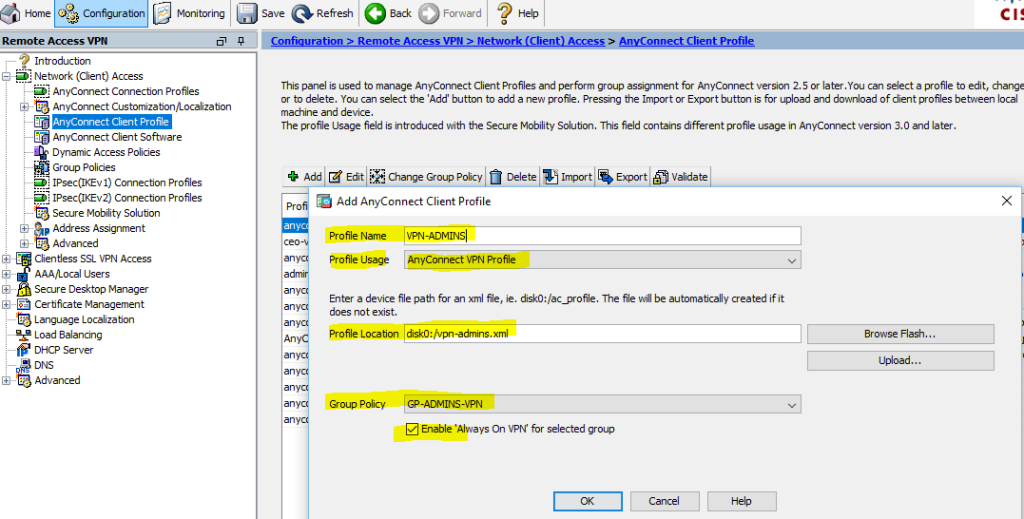
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Client Profile
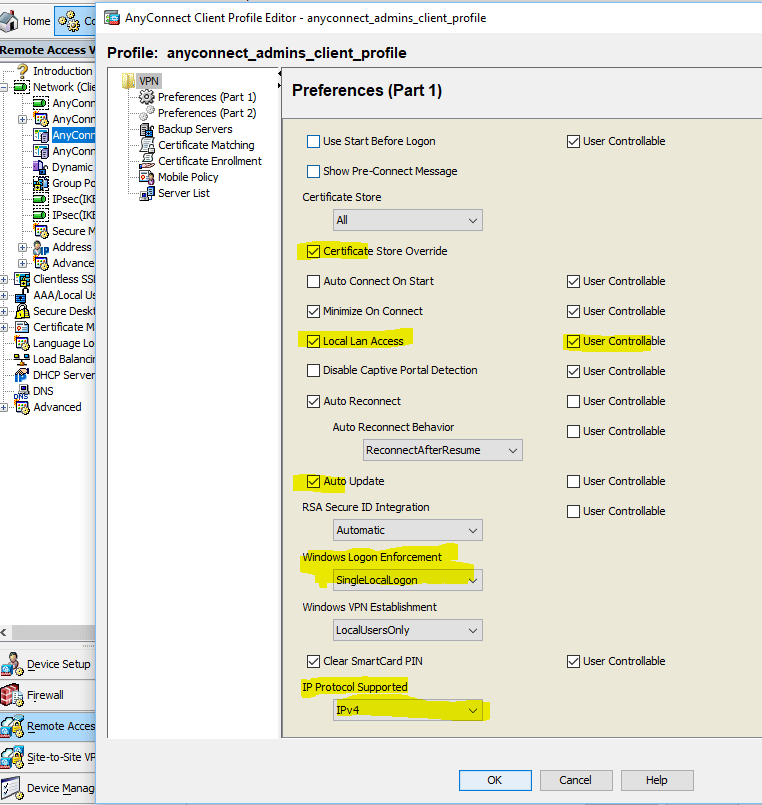
����� ����, ��� ������� �������� � ��� ����� ������� ���������������: ������� � ������� ��� �����"Local Lan Access"? ��� ��� ��� ����� �������������. � ��� ����� �� ����� ��������� ����� ��������� ������������, �������������� ������� AnyConnect, ���������\��������� ����������� ����������� � ����� ����� ���, ��� ������������ ���, ������� ������ ��������� (IPv4 or IPv6 or both, ��������� ������������ � ��������, ��������� ��������. � ����� ���� ��� ������������ ��� ���� �����!
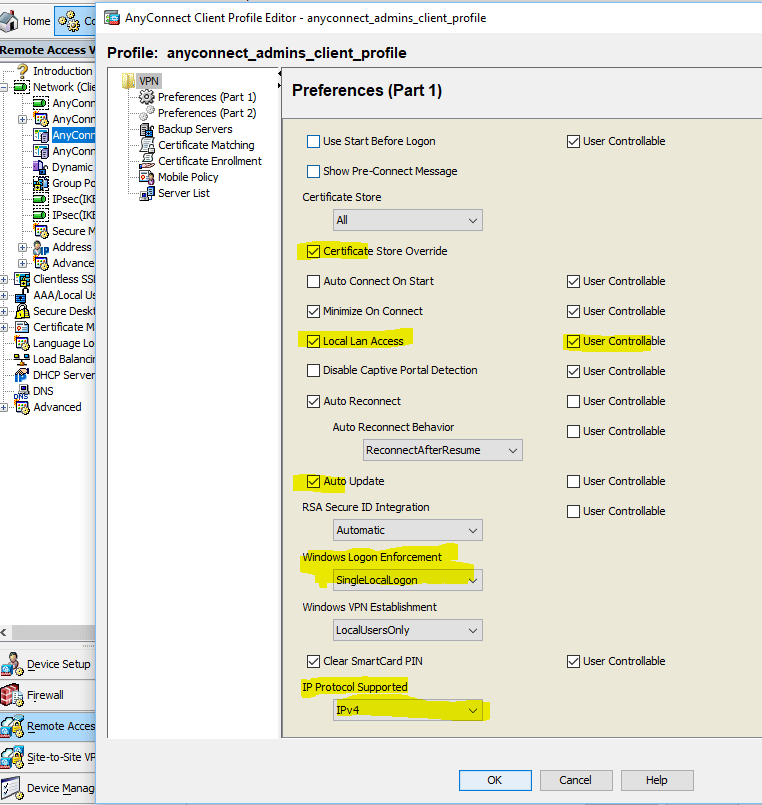
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Client Profile > Edit
��� ������ ������ � �VPN-USERS� ����������� ���� �����
P.S. ��� ��������� ������� � ������ ������������ �����
| �������������� | « ����. ������ — � �������� — ����. ������ » | ��������: [1] [�����] |






